Building a Secure QR-Based Employee Verification System Without a Database
How AuraDevs built a lightweight QR-based employee verification system using deterministic cryptography and server-side validation.
Building a Secure QR-Based Employee Verification System Without a Database
The problem is simple: Anyone can print a fake business card. Screenshots can be copied. ID badges can be replicated.
At AuraDevs, we needed a way to instantly verify employee identity with nothing more than a QR scan.
So we built a lightweight verification system using deterministic cryptography and server-side validation, no database required.
Here’s how it works and why it matters.
The Traditional Verification Problem
Most organizations verify employees through:
- Physical ID cards (easily forged)
- Email signatures (screenshots work)
- Manual HR confirmation (slow)
- Employee directories (anyone can screenshot)
None of these methods are cryptographically secure.
What we wanted was instant, tamper-proof verification that anyone could check — clients, event organizers, partners, or building security.
The Solution: Cryptographic QR Codes
Each employee gets a unique QR code that encodes a verification URL:
https://auradevs.co/v?i=anishbiswas&k=92cea30c51c1Where:
i= employee identifierk= cryptographic verification key
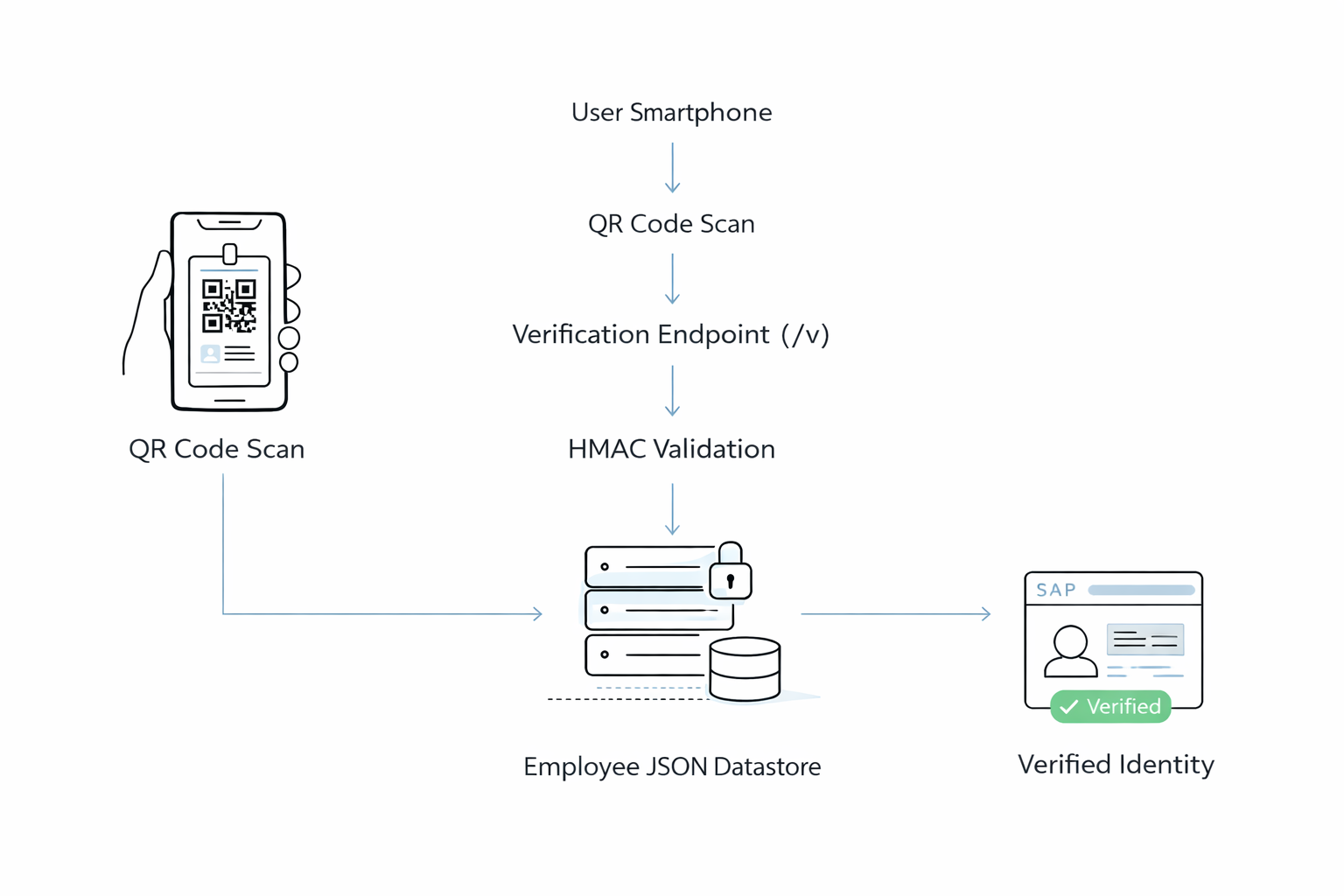
When someone scans this QR code:
- Server recomputes what the key should be
- Compares it with the provided key
- Instantly verifies or rejects the identity
No database lookup. No token storage. Just cryptographic math.
Why We Skipped the Database
Many verification systems rely on databases to store issued tokens or IDs. Instead, we chose a deterministic cryptographic model.
Advantages include:
- No database queries
- No synchronization issues
- No token storage
- Faster server responses
- Simpler infrastructure
The system relies on two things:
- A secret key stored on the server
- A predictable cryptographic function
Because the same input always produces the same output, we can validate tokens instantly.
The Security Model
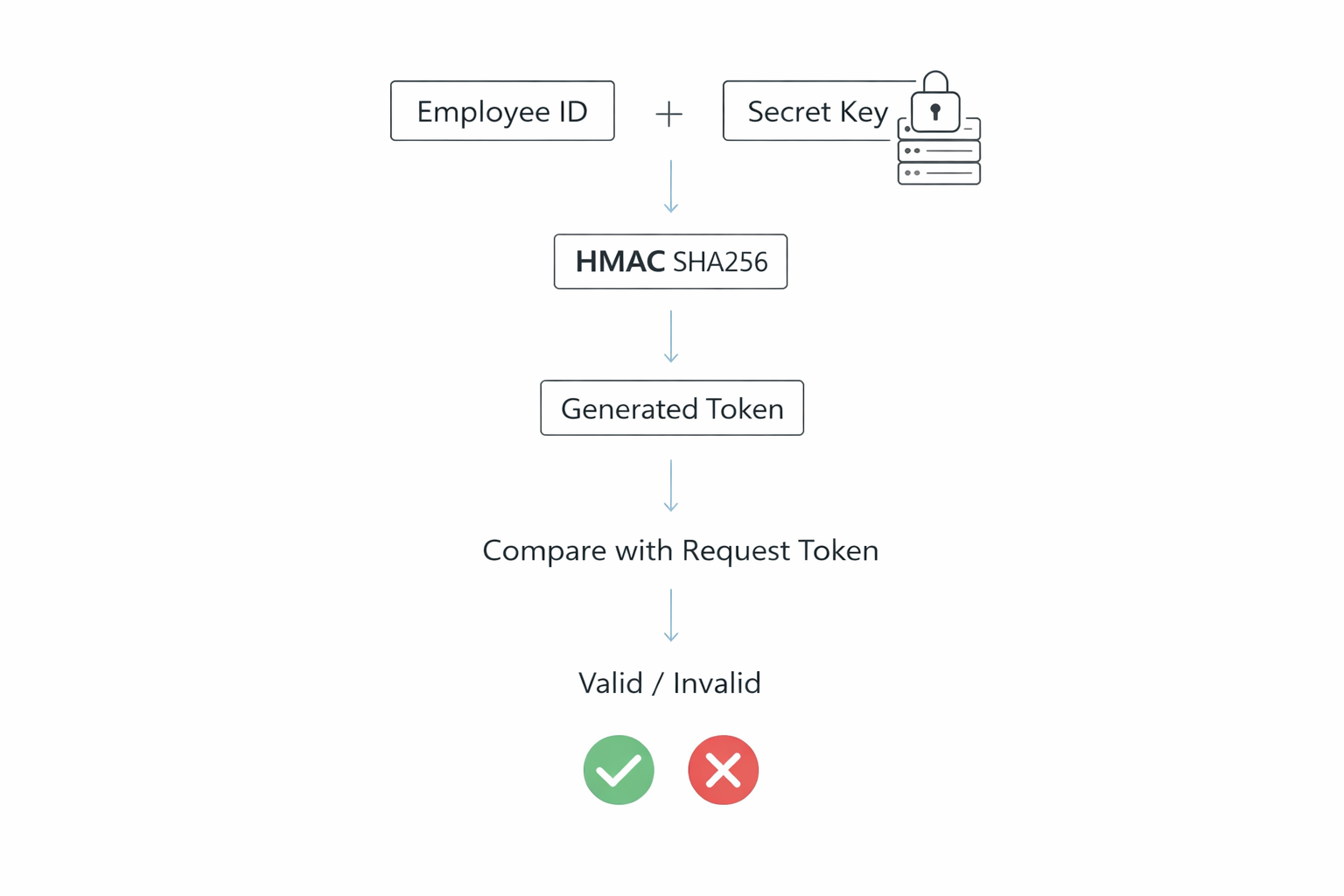
To ensure security, we use HMAC-SHA256. HMAC stands for Hash-based Message Authentication Code, which allows us to generate signatures using a secret key that only the server knows. It is battle-tested cryptography used in:
- JWT tokens
- API authentication
- Two-factor authentication
- TLS/SSL certificates
The verification key is generated like this:
HMAC(secret, "emp:{employeeId}:auradevs")This produces a long hexadecimal hash. For convenience, we truncate it to 12 characters, which is still extremely difficult to guess.
Example:
employeeId: anishbiswas
payload: emp:anishbiswas:auradevs
HMAC → 4f9c2a8e91d2Without knowing the secret key, generating a valid verification key is practically impossible.
Therefore the security it guarantees are:
- 12-character hex = 2⁴⁸ possible combinations
- Brute-forcing would take millions of years
- Even if someone guesses a key, they still need a matching employee entry
Implementation (20 Lines of Code)
Here’s the complete verification logic:
import crypto from "crypto";
import employees from "../data/employees.json";
const SECRET = process.env.EMPLOYEE_QR_SECRET;
function generateKey(employeeId) {
const payload = `emp:${employeeId}:auradevs`;
return crypto
.createHmac("sha256", SECRET)
.update(payload)
.digest("hex")
.slice(0, 12);
}
export function verifyEmployee(employeeId, key) {
const expected = generateKey(employeeId);
if (expected !== key) {
return null;
}
if (!employees[employeeId]) {
return null;
}
return employees[employeeId];
}That’s it. The entire verification system in less than 20 lines. This ensures the entire verification process happens securely on the server.
Data Storage: JSON Over Database
We maintain employee records in a simple JSON file:
{
"anishbiswas": {
"name": "Anish Biswas",
"role": "Co-founder & CEO",
"company": "AuraDevs"
},
"subhadeeproy": {
"name": "Subhadeep Roy",
"role": "Co-founder & CTO",
"company": "AuraDevs"
}
}Why JSON?
- Faster reads (no network latency)
- Version controlled with Git
- No database maintenance
- Perfect for teams under 1000 employees
- Easy to audit and update
Even if someone somehow guesses a valid key (virtually impossible), they still need to match an actual employee in our records.
The Verification Flow
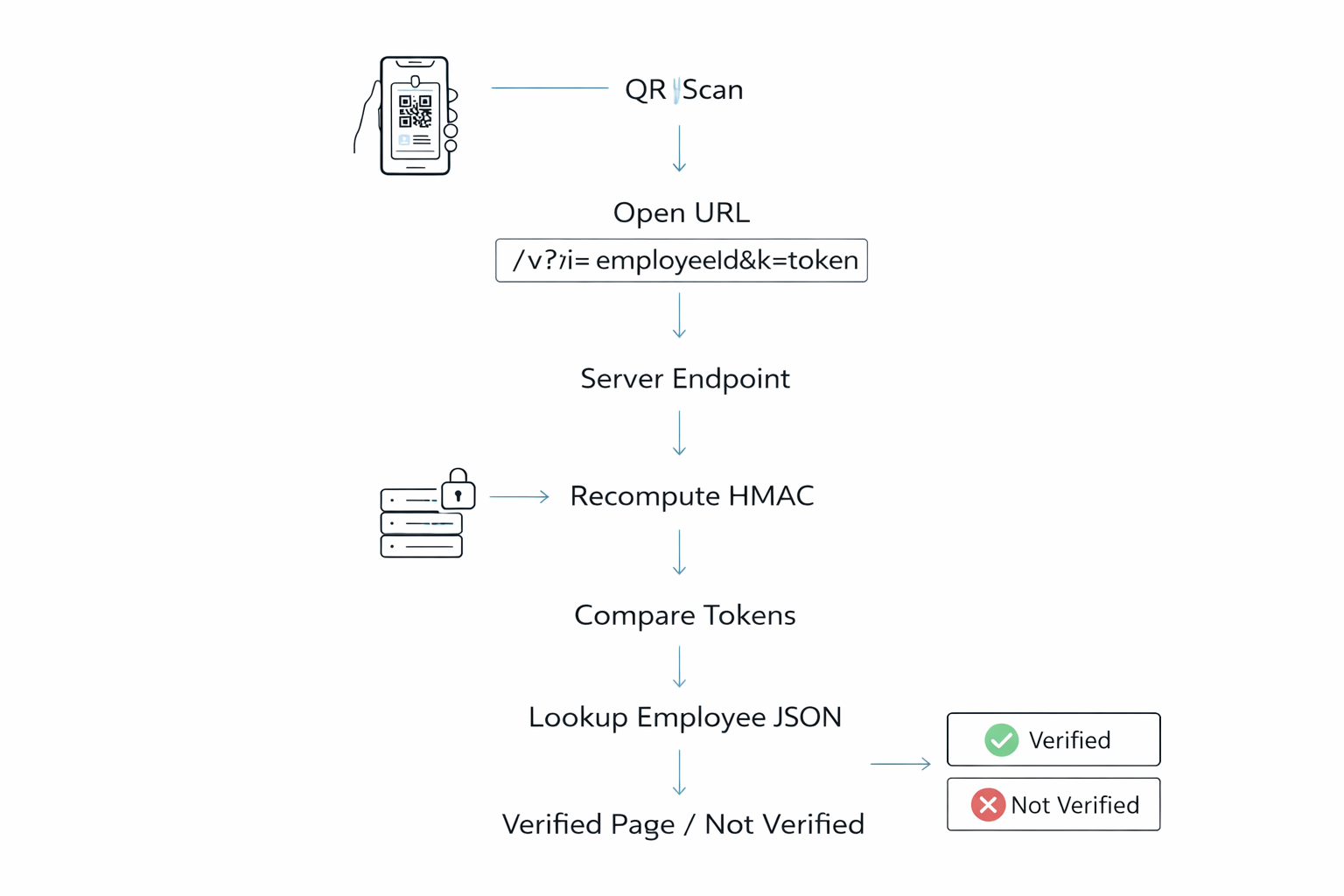
- Step 1: QR code scanned → opens
/v?i=employeeId&k=key - Step 2: Server recomputes expected key using secret + employee ID
- Step 3: Keys match? If no → ❌ Verification Failed
- Step 4: Employee exists in our records? If no → ❌ Not Found
- Step 5: Both checks pass → ✅ Verified Employee
Real-World Use Case: AuraDevs Business Cards
We implemented this on our business cards. Each team member carries a card with their contact info and a unique QR code for instant verification.
When someone scans it:
- They’re taken to our verification page
- Server validates the cryptographic signature
- They see the verified employee profile — name, role, company
This solves a real problem: Anyone can print a business card claiming to work at AuraDevs. But they can’t fake our cryptographic verification. Potential clients can instantly confirm they’re dealing with a real employee, not a scammer or impersonator.
Beyond Business Cards, this pattern works for:
- Event badges at conferences
- Contractor authentication
- Certificate validation (degrees, courses)
- Product authenticity checks
- Membership verification (gyms, clubs)
- Building access control
Any scenario requiring instant, tamper-proof verification.
Final Thoughts
Security systems do not always need heavy infrastructure.
Sometimes the most elegant solutions come from combining simple ideas:
- deterministic cryptography
- server-side verification
- minimal infrastructure
By implementing this system, we created a lightweight yet secure verification mechanism that scales easily while remaining simple to maintain.
At AuraDevs, we believe security doesn’t require complexity, it requires thoughtful engineering.
Want to implement this for your organization? We’d love to help. Reach out at office@auradevs.co. Check us out live at: auradevs.co
Share this insight
Join the conversation and spark new ideas.